Navigating Data Privacy and Security Trends and Emerging Technology
Amplitude
FEBRUARY 5, 2024
Explore trends and emerging technology to help you navigate today’s complex data privacy and security landscape.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

 data-privacy-security
data-privacy-security 
Amplitude
FEBRUARY 5, 2024
Explore trends and emerging technology to help you navigate today’s complex data privacy and security landscape.

Amplitude
JANUARY 28, 2024
A robust privacy and security culture does more than comply with regulatory standards—it shapes employees' everyday actions and decisions. Learn how to create a strong culture.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.
The Path to Product Excellence: Avoiding Common Pitfalls and Enhancing Communication
Peak Performance: Continuous Testing & Evaluation of LLM-Based Applications
From Developer Experience to Product Experience: How a Shared Focus Fuels Product Success
Understanding User Needs and Satisfying Them
Beyond the Basics of A/B Tests: Highly Innovative Experimentation Tactics You Need to Know

Pragmatic Marketing
AUGUST 20, 2019
Data Security Becoming Increasingly Important for Consumers With data breaches becoming increasingly common, consumers are realizing that their personal information is at the mercy of the organizations they’re doing business with—resulting in changing attitudes around security.
The Path to Product Excellence: Avoiding Common Pitfalls and Enhancing Communication
Peak Performance: Continuous Testing & Evaluation of LLM-Based Applications
From Developer Experience to Product Experience: How a Shared Focus Fuels Product Success
Understanding User Needs and Satisfying Them
Beyond the Basics of A/B Tests: Highly Innovative Experimentation Tactics You Need to Know
AB Tasty
DECEMBER 27, 2019
Hailing from GDPR’s home of Europe, AB Tasty believes in a secure, opted-in web that is optimized and personalized to enhance the user experience. Our algorithms, machine learning and experiments are all powered by data.

The Product Coalition
FEBRUARY 29, 2024
While this guide focuses on choosing LLMs for user-facing applications (think chatbots, writing assistants), remember they can also revolutionize internal tasks like report generation or data entry. Data Richness: A wealth of data opens doors to training bespoke models. LLMs like XLM-R excel in handling diverse languages.

Alchemer Mobile
NOVEMBER 14, 2023
Efficiently scale your app development with the Alchemer Digital API With the Alchemer Digital API for both Mobile and Web, you can seamlessly integrate real-time metrics and raw data into your reporting and business intelligence tools, connect data to your most important business systems, and safely share insights across your org.

Userpilot
MARCH 12, 2024
The growing number of applications used by employees must be carefully managed to optimize product engagement and maintain security. This article explores key tips and best practices to streamline your SaaS user management process and create a productive and secure work environment. Which tools do they use most?

Intercom, Inc.
MARCH 25, 2021
From healthcare providers to insurers and others, the pandemic is rapidly driving organizational change and prompting businesses to consider future needs by adopting new technologies to replace or assist with historically manual workflows without compromising on care or privacy. What is HIPAA? What does this mean for your business?
The Product Coalition
MARCH 4, 2024
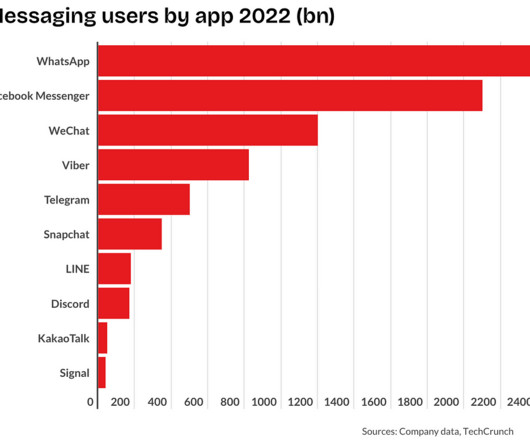
Its popularity was fueled by its commitment to user privacy, with end-to-end encryption ensuring that messages could only be read by the intended recipients. This commitment to privacy and security has been a cornerstone of WhatsApp’s success, earning the trust of users around the globe.

The Product Coalition
OCTOBER 11, 2023
Instead of one central authority (like the big shots at Facebook or Twitter), decentralized platforms use blockchain technology and independent servers to store your data. Crypto wallets are your ticket to create a profile while keeping your privacy intact. It’s an image-first social media platform with a strong focus on user privacy.

The Product Coalition
MARCH 3, 2024
Enter customer behavior prediction, a revolutionary approach that utilizes data and technology to forecast what your customers will do, buy, or feel in the future. In today’s competitive landscape, businesses are bombarded with data. But simply collecting data isn’t enough; the true power lies in unlocking its predictive potential.
The Product Coalition
OCTOBER 3, 2023
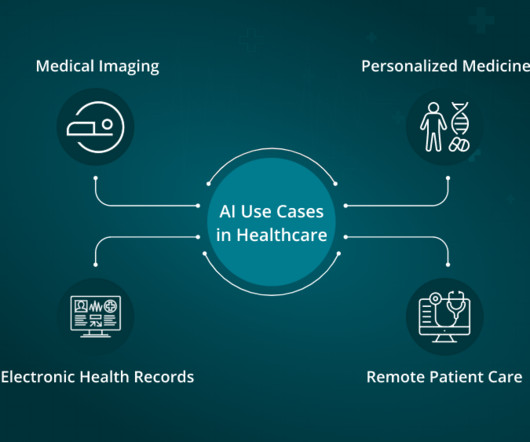
Patient data privacy: While it may seem counterintuitive, AI can also enhance patient data privacy by implementing robust security measures and access controls. Predictive models can assess patient data to identify individuals at risk of developing specific diseases, allowing for early intervention.

The Product Coalition
OCTOBER 8, 2023
Reliable Data Sources The foundation of any prediction platform lies in the quality and reliability of its data sources. To provide accurate forecasts, you must ensure access to real-time market data, historical trends, and sentiment analysis feeds. Diverse and dependable data streams are essential for robust predictions.
Intercom, Inc.
OCTOBER 19, 2022
Your data is our most critical asset. We protect it throughout its lifecycle with robust security practices, tailored role-specific staff training, and rigorous compliance with regulations. We handle the security of your data so that you can focus on acquiring, engaging, and retaining your customers. Expiry and deletion.

Userpilot
FEBRUARY 21, 2024
In SaaS, the top data analytics trends can either be a revolution or just fluff. So what are the trends in the data analytics landscape that are actually important for product management ? Edge computing : Processes data closer to its source, analyzing data faster, giving real-time insights, and reducing latency and network costs.

The Product Coalition
NOVEMBER 23, 2023
Machine Learning (ML) ML is a technique that enables computers to more efficiently process and interpret data. Data security and privacy Data security and privacy are two of the most difficult concerns in digital health. million patients affected by healthcare-related data breaches in 2021.

UX Planet
JANUARY 13, 2024
The Ethical Obligation: Transparency and Privacy Generation Z is more aware than ever of data privacy and ethical considerations. Expect businesses to handle their data responsibly. This places a responsibility on UX designers to prioritize privacy and security in their interfaces. They value transparency.

The Product Coalition
OCTOBER 4, 2023
Discover how DEXs are reshaping crypto trading, offering security, accessibility, and financial innovation. Security: DEXs are inherently more secure as they are less vulnerable to hacking attacks that typically target centralized exchanges. Embrace the future of finance today!

Alchemer Mobile
DECEMBER 22, 2020
We’ve grown accustomed to expect certain levels of personalization, speed, and security as we’re living out the majority of our lives digitally. Data and Security. In 2021, businesses will be investing more in cybersecurity in order to improve data protection and comply with information privacy laws. Conclusion.

Userpilot
APRIL 3, 2024
TL;DR Dashboards display critical business data in real-time, streamlining decision-making and focusing on key metrics. When choosing a dashboard tool, pay attention to the ease of use , customization, integrations , value, and data privacy to meet business needs effectively. What qualities to look for in dashboard software?
The Product Coalition
NOVEMBER 17, 2023
Think Facebook, Google, or Amazon — they control the data, the apps, and pretty much everything else. Your Data, Their Control: When you use Web2 services, your data is stored on their servers. You Own Your Data: With Web3, you’re in control of your data. No more digital overlords! You decide who sees what.

Intercom, Inc.
APRIL 23, 2018
When building your products, the security and privacy of your customers’ data needs to be a top priority. And that is also true when selling and marketing your product, particularly with the arrival of GDPR, which has brought the issue of data security and privacy to widespread public awareness.

The Product Coalition
MAY 9, 2023
It offers secure and transparent transactions without intermediaries, making it a popular choice for businesses looking to streamline their operations. While most people associate blockchain with public cryptocurrencies like Bitcoin, there are also private blockchain networks that are used by businesses to improve efficiency and security.

UX Planet
MARCH 17, 2024
The vast amount of data collected about us, often without explicit consent, has eroded user trust in transparency efforts. Prioritizing User Privacy & Data Protection Imagine using a fitness app that mysteriously starts bombarding you with ads for protein supplements after a single jog. They excel in ethical data practices.

The Product Coalition
JULY 7, 2023
These contracts are built on the principles of transparency, security, and efficiency, offering a revolutionary approach to traditional contractual arrangements. Blockchain provides a decentralized and distributed ledger, serving as the foundation for storing and validating contract data.
Intercom, Inc.
NOVEMBER 8, 2022
Our teams are dedicated to ensuring that Intercom achieves the scale, reliability, interoperability, and world-class standards of privacy and compliance that our customers need to deliver a stellar customer experience. In five chapters, you’ll learn all about: Intercom’s rigorous security measures. How we maintain high availability.

The Product Coalition
APRIL 1, 2022
They build trust in the data that is stored on the blockchain platform. Although, when we discuss blockchain technology as an enterprise-grade solution, it proves that organizations prefer to develop their applications via the industry-standard permissioned blockchains or the distributed ledger ecosystems for better privacy.
The Product Coalition
DECEMBER 6, 2021
Internet of Things (IoT) transforms formerly “dumb” gadgets into “smart” ones by allowing them to transfer data over the internet and connect with humans and other IoT-enabled devices. To initiate, you’ll want a device capable of gathering data in real-time. A nice example of IoT in action is the linked “smart house.”
Userpilot
APRIL 17, 2024
If you want to know more about your product , you need data. The more data you can capture about your customers, the better you can understand them and improve your product. Two methods of tracking customer data are implicit data event tracking and explicit tracking.
Intercom, Inc.
DECEMBER 6, 2022
Whether we’re creating tools that improve personalization or strengthening our privacy and security, Intercom has always been committed to bringing a personal touch to every change we make to our product. Improves trust, privacy, and security. Trust, privacy, and security thrives when we offer control to the user”.

The Product Coalition
MARCH 8, 2023
Healthcare data exchange refers to the sharing of patient health information between various stakeholders, including payers (insurance companies), life sciences (pharmaceutical and biotechnology companies), and providers (doctors, hospitals, and clinics).

Userpilot
MAY 16, 2023
Hyper-personalization uses real-time data to provide more contextual experiences and build loyal customers. You should build customer trust by ensuring data privacy. A frictionless and secure customer experience is one of the top customers’ needs. Kontentino welcome survey built with Userpilot.

The Product Coalition
AUGUST 9, 2023
Governments, corporations, and innovators are embracing its potential to redefine how we handle data, security, and transactions. Its decentralization magic is unlocking new ways to secure data, ensure transparency, and streamline operations. Diverse Applications: How Blockchain is Making Its Mark Beyond Cryptocurrencies?

TechEmpower - Product Management
JULY 24, 2023
What special data, content, APIs, etc., What’s the state of the relationships that brings you that data? Member Profiles What data is included? How does the application behave when location data is not available? What are your privacy rules? What is different, special here? Where’s the mystery?
Intercom, Inc.
FEBRUARY 22, 2022
At Intercom, we think deeply about how to deliver the safest, most secure experience possible for our customers and their customers. . As a SaaS business, Intercom is a data processor: our customers entrust us with their data, which we store and process on their behalf. Shipping quickly and securely.
Userpilot
JANUARY 14, 2024
The main challenges for PMs are going to revolve around the increasingly competitive landscape, data privacy and security concerns, and financial constraints. With modern product analytics tools , it’s super-easy to access detailed data on user interactions with the product to make informed decisions.
Intercom, Inc.
JULY 15, 2022
If you’re online, so is your data and your customers’ data, which must be protected. Going further than that, your customers have to trust you with that data. How do you keep your business secure and also build and maintain the trust of your customers? Secure your teammate logins with 2FA, SSO, or SAML.

The Product Coalition
MAY 27, 2022
As blockchain is decentralized, it means the entire data is secured and updated across more than thousands of computers across the world, different from the centralized activity where the data is being stored in a single server. The decentralized nature makes it harder to steal value or hack data.

Userpilot
APRIL 16, 2024
Also, collect qualitative data through surveys to understand users better. This data helps eliminate friction points from the user journey. Create data-driven product strategies – End-user behavior analytics takes the guesswork out of product development. To analyze user behavior, define the user persona first.

Modus Create
FEBRUARY 16, 2024
Users increasingly demand and expect information privacy and robust encryption methods. But it’s difficult for organizations to keep up with security , particularly as they’ve accrued debt by outpacing spending on other initiatives over security. As a result, cybersecurity has become a top challenge for many companies.

The Product Coalition
JULY 11, 2023
With blockchain, transactions can be processed and settled more quickly and securely. These nodes work together to maintain the integrity and security of the network. Cryptocurrencies are digital or virtual currencies that leverage cryptographic technology to secure transactions and control the creation of new units.
The Product Coalition
JUNE 11, 2023
Prioritize Privacy and Security Ginger Healthcare apps deal with sensitive personal information. Assure users that their sensitive health data is secure by clearly communicating the security measures in place during the onboarding process. Make sure users understand their rights and how their data will be used.

Valerian Tech
JUNE 19, 2023
Introduction In today's digital age, healthcare companies face increasing threats to the security and privacy of patient data. The potential consequences of data breaches, such as financial losses, reputational damage, and loss of patient trust, highlight the critical importance of robust data security measures.

Valerian Tech
JUNE 5, 2023
With the rising frequency and sophistication of cyber threats, safeguarding sensitive customer data and protecting against potential breaches is of paramount importance. Protecting this data from cyber threats is crucial for maintaining customer trust and complying with stringent data protection regulations.
Expert insights. Personalized for you.
Are you sure you want to cancel your subscriptions?

Let's personalize your content